The now infamous "WannaCry" ransom-ware virus has been making headlines and scaring a lot of computer users around the world. It is one of the quickest spreading Ransom-ware bugs that has been released to date, but Ransom-ware viruses are not anything new.
Ransom-ware viruses are a type of virus that infect computers, and then prevent the user from accessing the operating system, or encrypting all the data stored on the computer. Then the user is asked to pay a fixed amount of money as ransom to unlock their files, allowing them to regain access to the operating system and their data again. What sets this virus apart is how quickly and widely it has spread.
As of yesterday a Security Professional, Marcus Hutchins, has been credited with stopping the WannaCry ransomware attack from spreading across the globe, by accidentally triggering a "kill switch" found in reverse engineering the virus. So for now, further infection has been stopped. But to prevent any infections from previous distributions of the bug you can do the following:
"WannaCry" Ransomware Guidelines to Stay Safe:
- Be careful to NOT click on harmful links in your emails!
- Even with security software installed, if you open/download an attachment from a malicious email it can and will infect a computer and network!
- If you get an email from someone, look at the email address/email header and make sure it's from who it says it is.
- Be aware of fraudulent e-mail messages that use names similar to popular services such as PayPal instead of PayPal or use popular service names without commas or excessive characters.
- Be wary of visiting unsafe or unreliable sites
- Never click on a link that you do not trust on a web page or access to Facebook or messaging applications such as WatSab and other applications.
- If you receive a message from your friend with a link, ask him before opening the link to confirm, (infected machines send random messages with links).
- Always make have the latest update for your Antivirus; Let me know if there are any update issues!
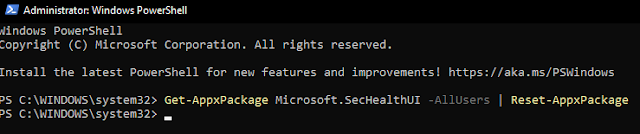
- Make sure your windows have the latest updates to close the gap!
- If windows has reported that updates are pending/available; download and install immediately!!
Further Steps to take in-case you WERE to get infected by the "WannaCry":
- Make a recovery disk! The WannaCry ransomware asks for $300 or more if you a modified version if you do not pay the creators (in Bitcoin to its untraceable and not refundable) encrypt all of your files on the computer.
- If your computer gets infected take it off of your network immediately! The ransomware will spread to other computers on the network! You can restore from a backup.
- If you would like our assistance with ANY of the procedures above or would like us to secure your computer and/or network to the best of it's ability, let us know and we can schedule an onsite or remote session for you!!
More from Microsoft on the bug and associated patches to help prevent infections from WannaCry:
https://technet.microsoft.com/…/libr…/security/ms17-010.aspx
Jon-Eric Pienkowski
_________________________
Pacific NorthWest Computers
(360) 624-7379






.jpg)
.jpg)